CloudFlare and CloudBleed
Our beloved CloudFlare has very rapidly patched a bug in their HTML parser, which allows for random bits of private data to be exposed via other CloudFlare patrons’ websites. This is also being cached by search engines! This is not good!
While search engines are working fervently to mitigate this mishap, it leaves webmasters holding the bag. If you’re a webmaster and you’re reading this, there are some very important things you need to know if you use CloudFlare.
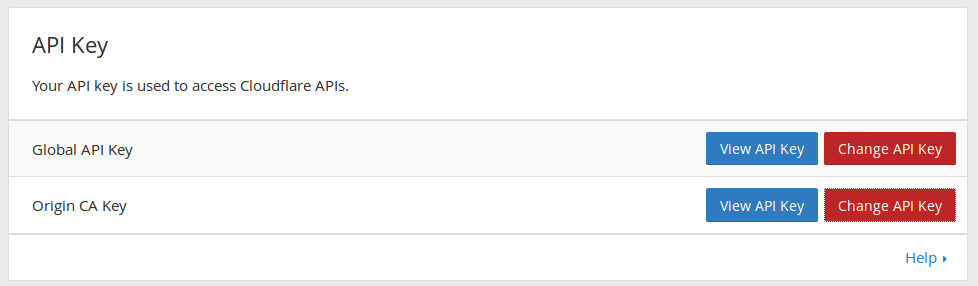
API Keys
Any application or API that utilized an API key that was transmitted to a host behind CloudFlare will likely need to be changed. The reason behind this is that it could potentially have been compromised, as the problem has existed for the past 6 months! Now that the bug is patched on CloudFlare’s end, it’s up to the webmaster to change passwords and affected API keys.
Passwords
Any kind of plaintext password that was transmitted (even over SSL) to a CloudFlare proxied site will need to be updated. It’s possible that the bug exposed this via random output on another CloudFlare site. Many have been scraping this data for months for some quite interesting intel.
App Secrets
If you use any kind of password salting for your passwords, session cookies, or even generic or httponly cookies, you will want to rotate and randomize these keys. After you do this, issue forced password resets for your admins, then your users.
2 Factor Authentication
This shouldn’t have to be said, but for anything very important, you should have a method to verify your password out-of-band. A lot of providers support 2FA, short for 2 Factor Authentication. There exists MFA for Multi-factor, which supports more than 2 methods to authenticate, but that’s for another blog post.
Using the Google Authenticator app, you can assign a One Time passcode that changes every 60 seconds to verify your sign-in. CloudFlare and Google both do this. Go now and enable it, i’ll wait.
You can change your CloudFlare account password in Settings on the top right, then scroll down to the following sections:
Conclusion
Hopefully this notice helps someone, though it does not appear that anyone has exploit this vulnerability in the wild, though it makes me feel a little safer. Comments and questions are open!